Registry Editor, a main registry editing tool equipped in all versions and editions of Windows operating system, can be disabled, blocked and locked to prevent the RegEdit from been ran or executed by users in order to protect important system registry. Other possibility of Registry Editor been disabled is caused by virus or worm such as W32/Brontok-C.
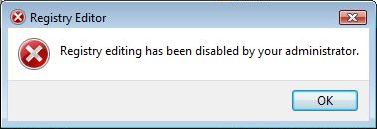
When Registry Editor is disabled, user unable and cannot open or run Registry Editor anymore. Any attempt to run RegEdit.exe will return the error “Registry editing has been disabled by your administrator”. Hence it’s impossible to remove the restriction on Registry Editor usage by using the Registry Editor itself. However, it’s possible to use various workaround to directly edit the registry to remove the policy that blocks Registry Editor usage.
Enable Registry Editor using Local Group Policy Editor
For user using Windows XP Professional, Windows Vista Ultimate, Windows Server 2003 or 2008 with Local Group Policy Editor and has access to an administrative user account, user can change the registry editor options in the Local Group Policy Editor.
- Click on Start -> Run (or Start Search in Windows Vista).
- Enter GPEdit.msc and then press Enter.
- Navigate to the following location:
User Configuration -> Administrative Templates -> System
- In the Settings pane, locate the Prevent access to registry editing tools option, and then double-click on it to open the settings dialog.
- Select Disabled or Not Configured.
- Click on OK button.
- Try to run RegEdit.exe, and if required (still blocking yet), restart the computer.
VBS Script to Enable or Disable Registry Editor
Doug Knox has created a .vbs VB script that able to toggle between enable or disable the Registry Editor. Right click to download and save the regtools.vbs into a folder. Then double click on the VBS file to run it.
The regtools.vbs VB script file will check for the appropriate value related to disabling/enabling of Registry Editor. If the registry key is not found, the key will be created to disable Registry Editor. If the value was found, it will be toggled to its opposite state and you will be informed that you need to log off and log back on or restart your computer. All change by the script is made in HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System.
UnHookExec.inf by Symantec to Reset Registry Values to Default Settings
In many cases, disabling of Registry Editor is caused by virus, worm or Trojan, which attempts to stop user from fixing any changes to the registry, which normally affects changes to one or more of the shell\open\command keys. For example, exefile\shell\open\command key is changed, the virus, worm or Trojan threat will run each time that system run any .exe file. As such, Symantec create a .inf script tool to reset these registry values to their default settings.
WARNING: The UnHookExec.inf will reset registry keys and values related to BAT, COM, EXE, PIF, REG and SCR extensions, beside re-enabling the Registry Editor. Hence, users who just want to re-enable the Registry Editor has to manually modify the .inf file to remove the unnecessary commands.
Download the file UnHookExec.inf and save it to your Windows desktop.
Right-click the UnHookExec.inf file and click install. Action will be taken immediately. No display, nor any notice or boxes will appear before or after running. Try to run RegEdit.exe again, restart and reboot PC if it’s still blocked.