Jetico Personal Firewall Version 2.0.0.35 is recently released. It is a pretty effective security program that protects your computer from being attacked by hackers externally and bars disturbance from malicious programs that hide inside your computer’s memory and hard drive internally. This security software gives you three levels of protection: low-level network packets filtering, application-level network events filtering and filtering of user-level processing activity. This personal firewall will check every packet that flows in or out of your computer. It comes with a lot of excellent built-in documentation and it is quite a useful budget security solution. Having said that, this application is not so suitable for internet newbies or users who don’t really understand how applications and devices interact with the internet. This is because Jetico Personal Firewall will require you to do some configuration before using it. The wrong configuration might prevent you from running your other applications.
Jetico Personal Firewall’s 30-day trial version can be downloaded free of charge. Get the 3.2MB installation kit from Jetico download centre. As usual, after installing it, you will be led to Jetico Personal Firewall Configuration Wizard. You can configure your firewall step by step via the wizard. Once it is done, you need to restart your PC. You will thence be directed to the Jetico Personal Firewall window. There are 5 tabs there: Network Traffic, Application, Log, Group and Configuration. The Network Traffic Area will display to you a graphical view of incoming and outgoing traffic. In the Applications area, you will find the running programs and details about their network and internet connections. You can customize items shown there by right clicking on the bar containing their names and check/unchecking them using the contextual menu that appears. In the Log area, you can see every system event being monitored. The Groups are used by the program as parameter values for the firewall’s rules. Creating new groups and editing existing ones is as easy as it gets, and if you run into any problem, you can use the excellent documentation that comes with the program. In the Configuration area, you can make adjustment to filtering settings. However, if you don’t want to waste time on individual programs, you can block or allow the traffic by applying some general rules.
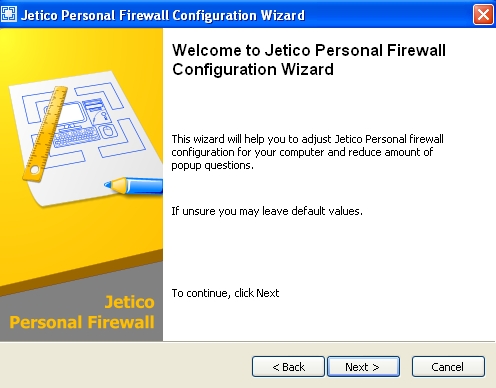
Jetico Personal Firewall Setup Wizard
Although it takes a bit of your time and effort for configuration, Jetico Personal Firewall is quite useful and helpful overall. So what is new in this latest release? Jetico Personal Firewall offers a number of new features as follows:-
Removed features
• Windows 9x/Me system support discontinued. Please use Jetico Personal Firewall v1 for these systems.
System-related changes
• Jetico Personal Firewall v2 runs as privileged Windows service. It can protect computer before user logon.
• Native support for Windows XP Fast User Switching and Terminal Services.
• Jetico Personal Firewall supports Access Control Lists for all main functions. Administrator can configure ACL to grant access to particular firewall functions for any user or group.
• Windows XP Service Pack 2 Security Center support.
User interface changes
• Improved rule editing interface.
• New popup message. The new look for popup dialog is presented. Popup message text and rule creation options can be modified.
• Firewall variables formerly controlled by Configuration Wizard, are integrated into main application window.
• Language file support for easy localization. All translatable words and phrases are taken from single UTF-8 encoded text file.
Configuration changes
• New XML-based open configuration file format. Detailed documentation is available upon request.
• The new version maintains single protected firewall configuration for all users.
• Simplified controls for configuration.
• New hash handling scheme. Separate table for hash checking.
• Each firewall filtering layer has own root table.
• New automatic variables (per-connection) for local connections are supported.
Changes in firewall rules
• Rules support lists of parameters where possible.
• IP rules support IP address ranges.
• Low level protocol rules support filtering by MAC address.
• Application rules have events for direct and indirect access to network. Indirect access details are also available.
• New module for hash checking created.
• Application, Process attack and Hash checking rules support wildcards in file paths.
Logging subsystem changes
• Log entries can be associated with rule.
• Firewall can create rule based on log information.
• New WELF-compatible text log format. WELF is supported by many log analyzers.
Download Jetico Personal Firewall v.2.0.0.35 for 32/64-bit Windows 2000/XP/2003/Vista. There is also a freeware Jetico Personal Firewall v.1.0 for Windows 98/ME/NT/2000/XP.
Recent Posts
- Able2Extract Professional 11 Review – A Powerful PDF Tool
- How to Install Windows 10 & Windows 8.1 with Local Account (Bypass Microsoft Account Sign In)
- How to Upgrade CentOS/Red Hat/Fedora Linux Kernel (cPanel WHM)
- How to Install Popcorn Time Movies & TV Shows Streaming App on iOS (iPhone & iPad) With No Jailbreak
- Stream & Watch Free Torrent Movies & TV Series on iOS with Movie Box (No Jailbreak)
 Tip and Trick
Tip and Trick
- How To Download HBO Shows On iPhone, iPad Through Apple TV App
- Windows 10 Insider Preview Build 19025 (20H1) for PC Official Available for Insiders in Fast Ring – Here’s What’s News, Fixes, and Enhancement Changelog
- Kaspersky Total Security 2020 Free Download With License Serial Key
- Steganos Privacy Suite 19 Free Download With Genuine License Key
- Zemana AntiMalware Premium Free Download For Limited Time